This blog will be about how to wipe or reset your Windows 10 Device the scripted way when you are (not yet) using Intune.
1. Background information
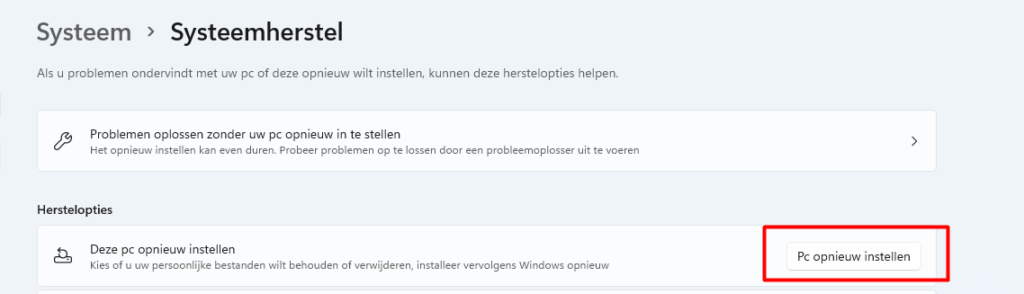
Of course, when you want to wipe or reset an existing, non-Intune MDM-enrolled device, you can run Systemreset.exe or do a reset manually.
Some time ago, I tested the possibility of resetting your device with the MDM Bridge WMI Provider.
It works great… But starting Powershell as an admin and elevating the PowerShell session to the system account took time. Also, I wanted to export the autopilot info at the same time without prompting for a username and password.
2.The PowerShell Way!
So, to automate it and make it easier for the customer, I created a Powershell script that did the same with only 1 UAC prompt.
The PowerShell script has three parts
- Reset Device WMI Part
- Autopilot export and Email (or auto-upload) part
- Downloading Sysinternal Tools and extracting it
It just starts the script and creates two scripts. It runs the first script as admin (UAC prompt) and, after the first script, the second script (Reset Device) as system.
It’s not the nicest script, but it gets the job done. You can also create a Flow to automate the autopilot part. And you can also create a nice “GUI” instead of the script to make it look better.
1. Wipe Device WMI PART
#MDM WMI Bridge part
$reset =
@’
$namespaceName = “root\cimv2\mdm\dmmap”
$className = “MDM_RemoteWipe”
$methodName = “doWipeMethod”
$session = New-CimSession
$params = New-Object Microsoft.Management.Infrastructure.CimMethodParametersCollection
$param = [Microsoft.Management.Infrastructure.CimMethodParameter]::Create(“param”, “”, “String”, “In”)
$params.Add($param)
$instance = Get-CimInstance -Namespace $namespaceName -ClassName $className -Filter “ParentID=’./Vendor/MSFT’ and InstanceID=’RemoteWipe'”
$session.InvokeMethod($namespaceName, $instance, $methodName, $params)
‘@2. Autopilot Export and Email the CSV
$start =
@’
$ProgressPreference = "SilentlyContinue"
$ErrorActionPreference= 'silentlycontinue'
$OriginalPref = $ProgressPreference
New-Item -Path c:\programdata\customscripts -ItemType Directory -Force -Confirm:$false | out-null
install-packageprovider -name nuget -minimumversion 2.8.5.201 -force | out-null
Save-Script -Name Get-WindowsAutoPilotInfo -Path c:\ProgramData\CustomScripts -force | out-null
Autopilot Info Uploaden
Upload-WindowsAutopilotDeviceInfo -TenantName $tenantname -OrderIdentifier "AADUserDriven" -Verbose
start-sleep -s 10
c:\ProgramData\CustomScripts\Get-WindowsAutoPilotInfo.ps1 -OutputFile c:\ProgramData\CustomScripts\MyComputer.csv
$PCName = $env:COMPUTERNAME
$EmailBody = $event
$EmailFrom = "$PCName@domeinnaam.nl"
$EmailTo = "autopilot@domeinnaam.nl"
$EmailSubject = "Autopilot CSV”
$SMTPServer = "tennantname.onmicrosoft.com"
Write-host "Sending Email"
Send-MailMessage -From $EmailFrom -To $EmailTo -Subject $EmailSubject -SmtpServer $SMTPServer -Attachments c:\ProgramData\CustomScripts\mycomputer.csv
#Start PowerShell session as system
Start-Process -FilePath "c:\ProgramData\CustomScripts\pstools\psexec.exe" -windowstyle hidden -ArgumentList '-i -s cmd /c "powershell.exe -ExecutionPolicy Bypass -file c:\programdata\customscripts\reset.ps1"'
‘@3. Downloading Sysinternals and Starting the script as system
#Export script to programdata folder
Out-File -FilePath $(Join-Path $env:ProgramData CustomScripts\reset.ps1) -Encoding unicode -Force -InputObject $reset -Confirm:$false
Out-File -FilePath $(Join-Path $env:ProgramData CustomScripts\start.ps1) -Encoding unicode -Force -InputObject $start -Confirm:$false
#Accepteula Psexec
reg.exe ADD HKCU\Software\Sysinternals /v EulaAccepted /t REG_DWORD /d 1 /f | out-null
#Sysinternals download part
invoke-webrequest -uri: "https://download.sysinternals.com/files/SysinternalsSuite.zip" -outfile "c:\programdata\customscripts\pstools.zip" | out-null
Expand-Archive c:\programdata\customscripts\pstools.zip -DestinationPath c:\programdata\customscripts\pstools -force | out-null
#Start Powershell Script as Admin
Start-Process powershell -ArgumentList '-noprofile -file c:\programdata\customscripts\start.ps1' -verb RunAsNow we have seen the three parts, add them all together in one script and deploy it to your users.
Conclusion
With this PowerShell script, you can easily perform a remote wipe of your devices even when they are not yet in Intune!


Could you give me a more explanatory tutorial? I tried to run the powershell with this script, but you don’t understand what it does and if it really worked, could you help me?
Hi, i did a blog after this one called: remote wipe the next level… maybe this one could help you further…
To be short: the powershell calls up on the the wmi bridge to make use of the csp to reset/wipe the device… (psexec is needed thats why i am downloading it in the script)
More details about how this works available at MS site, where they provide the WMi code that our wonderful author here has turned into something much more usable! Awesome info.
Happen to have a link for it …?