This blog will be about my test drive with the named location preview based on the GPS location.
I hoped this new feature could add some more security. First I will explain what I wanted to accomplish.
I was under the impression I could create a new conditional access policy, just like a conditional access policy where you block all countries except the countries in the “allow list”
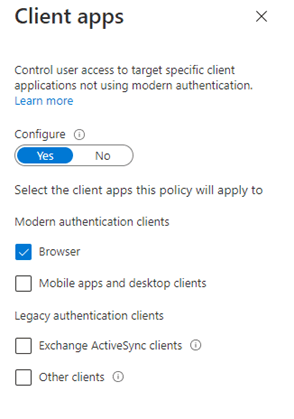
I wanted to add some security when a user uses a browser to access Microsoft 365 from a non-compliant device.
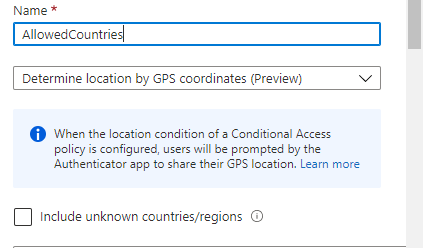
First I configured the Named locations and selected: Determine location by GPS coordinates. (preview)

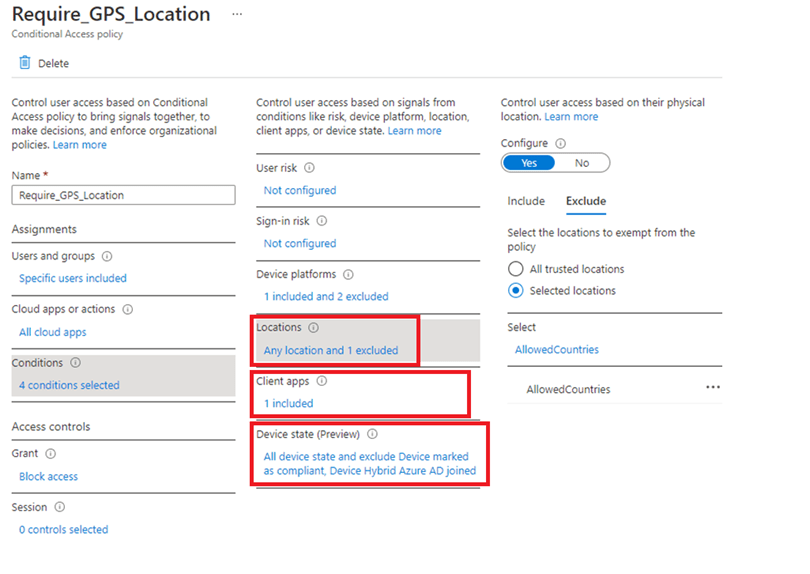
I made sure I excluded the named location, I just created. And just like I told you earlier, I don’t want compliant devices and desktop apps to prompt for the location. So I configured the policy to only apply to the browser and excluded device marked as compliant. Also, we don’t allow non-compliant devices to get access to Microsoft 365 with desktop apps.
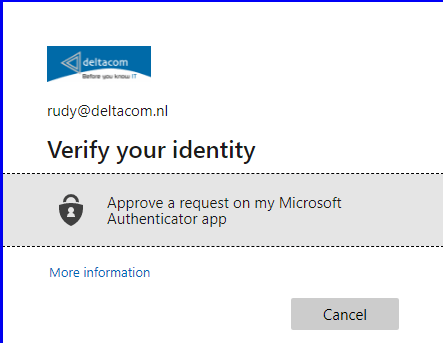
Within a few minutes after adding the conditional access rule, I opened a browser on a non compliant device to access Microsoft 365. Of course it prompted me for MFA first. After approving it asked me to “approve a request on my Microsoft authenticator app”
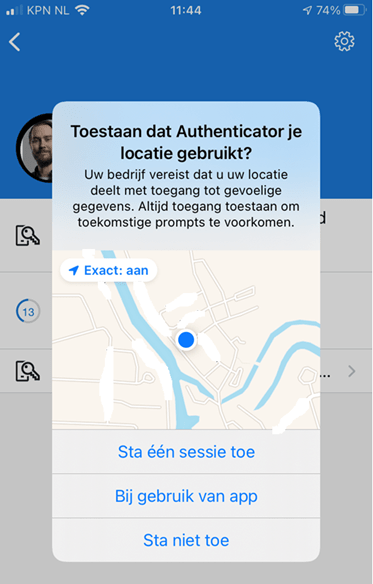
It asked me for my location… just like expected and asked me to allow to share my location with my company.
After approving and sharing my location I had access to Microsoft 365 from a non-compliant device while using the edge browser.
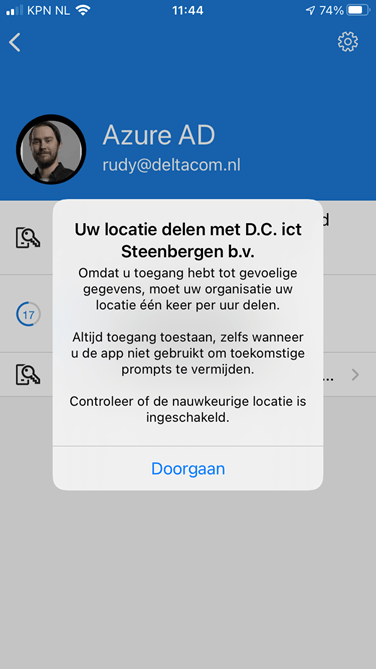
But at the same time, all my desktop apps on all my compliant devices “died”. Teams/Outlook on my mobile phone were also prompting me to share my location.
That’s some odd behaviour because I really excluded compliant devices and only targeted the browser. The dude abides. I don’t know about you, but I take comfort in that. It’s good knowing excluding won’t work.
I also tried the other way around. Instead of excluding the approved countries and make sure the CA rule was set to block, I included the approved countries and configured the CA rule to grant access and require MFA. But it resulted in the same experience… Location prompts on desktop apps on compliant devices.
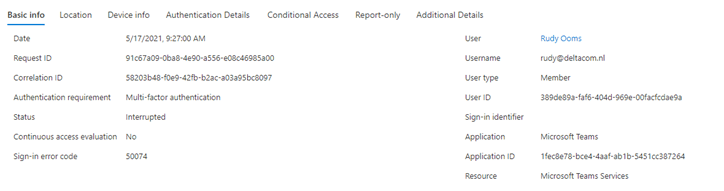
Looking at the sign-in log in Azure also did not showed me useful information, only: Interrupted
Conclusion:
I really like the idea to pinpoint your location by using the GPS function but I guess for now (I guess that’s why it’s also a preview) you can’t exclude stuff in your conditional access policy. Maybe I am trying something which is not the way Microsoft intended it. I guess deploying this without properly testing it would give some negative user experience.