This blog will hopefully show you some inside information on what issues you could run into when using AMD TPM attestation and Windows Autopilot for pre-provisioned deployments!
1. The famous AIK does not exist error
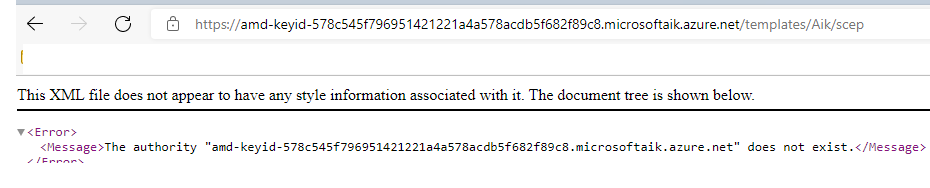
There are a lot of different error codes we need to beware of that you could run into when your AMD devices are giving you a time-out during TPM attestation. You would probably notice one of these errors: Something Went Wrong or 0x81039024 or, The authority and-keyed-578c545f796951421221a4a578acdb5f682f89c8.microsoftaik.azure.net does not exist.
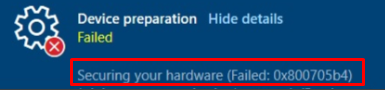
Not to forget the error 0x800705b4 you could receive during the “Securing your Hardware” phase
Let’s start with taking a good look at the CertReq_enrollaik_output.txt file first because troubleshooting TPM attestation errors will begin with running the mdmdiagnosticstool!
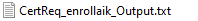
When you have exported the log, open it and I guess everyone that is trying to perform a white glove ahh damn… Windows Autopilot for pre-provisioned deployments… (WAPD from now on) will see the same AIK url failing
So what’s up with that? It seems a bit strange that this AIK service URL is failing for everyone, right?
2. Taking a better look at the AMD Ekcert
In the TPM happyness bog series part 2 I was showing you, how you could export this EKCert.
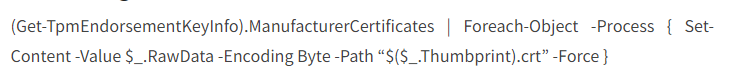
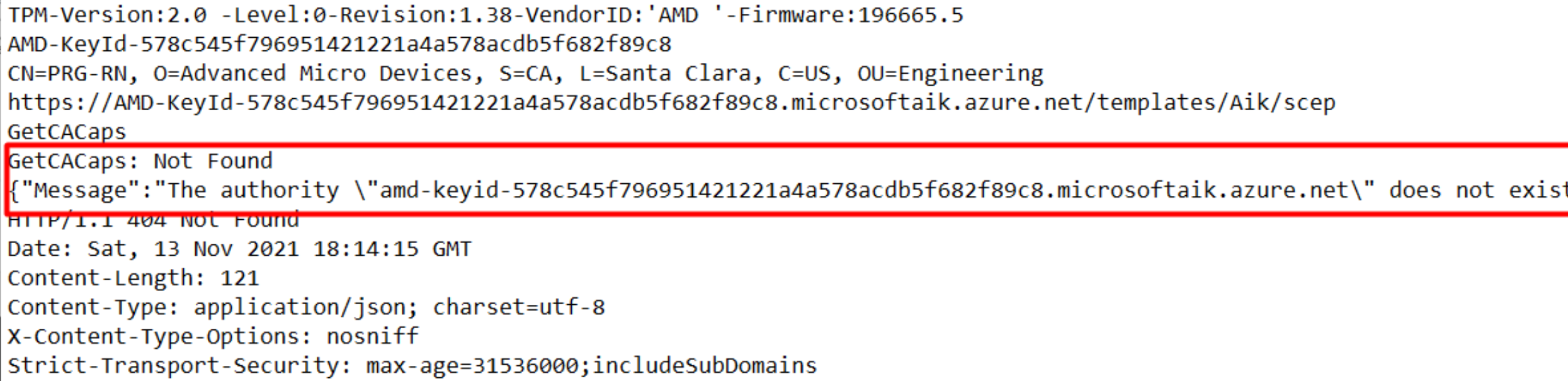
The command line for exporting the EKCert on an AMD device is different.
(Get-TpmEndorsementKeyInfo).AdditionalCertificates | Foreach-Object -Process { Set-Content -Value $_.RawData -Encoding Byte -Path “$($_.Thumbprint).crt” -Force }
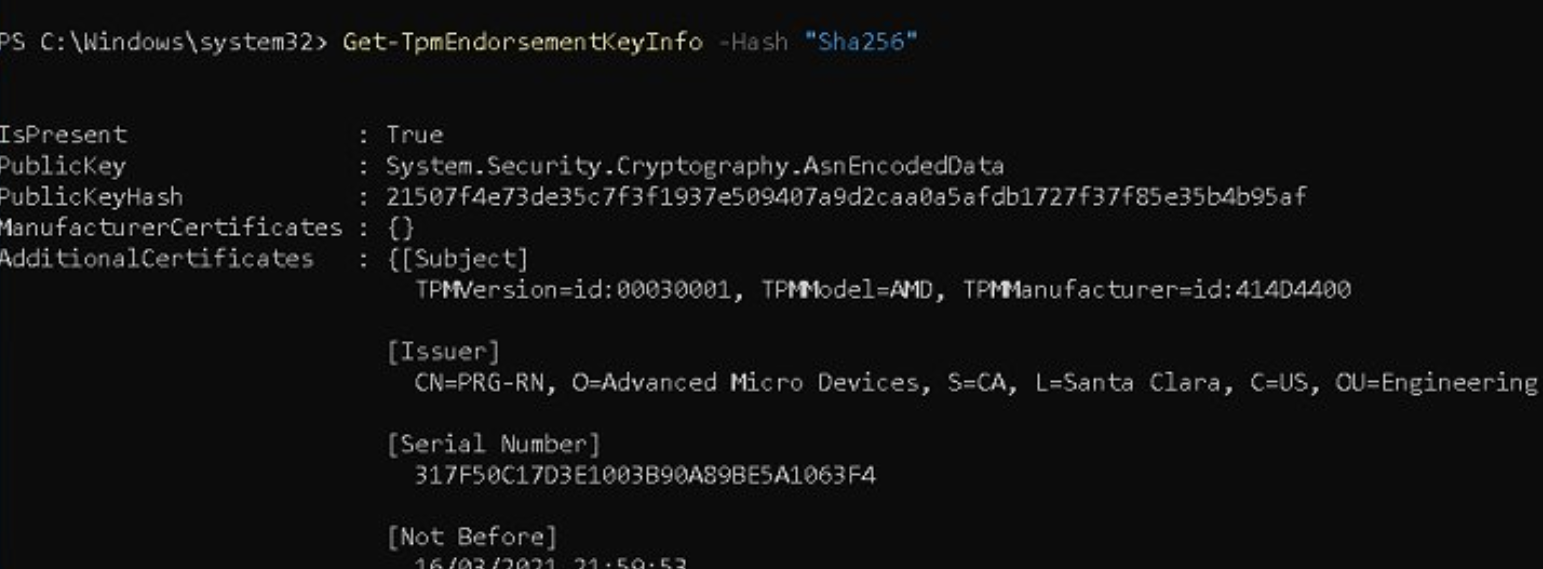
You could see it yourself using this command: get-TpmEndorsementKeyInfo -hash “sha256”. Instead of ManufacturerCertificates you will notice the AdditionalCertificates
Now let’s take a look at the EK certificate itself
That’s a whole other Certificate Authority (CA) then we noticed earlier of course!
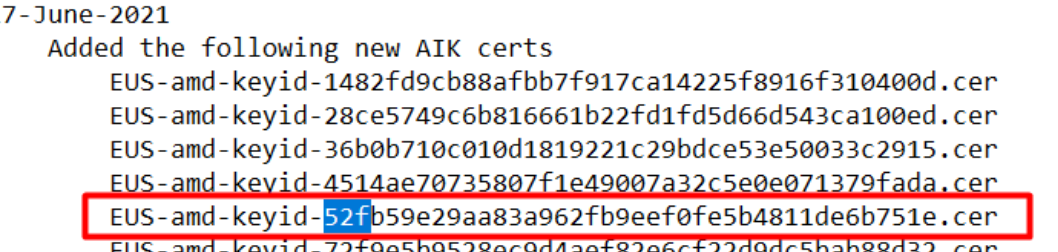
3. Taking a better look at the Key-IDS
So we have 2 CA Issuer ids.
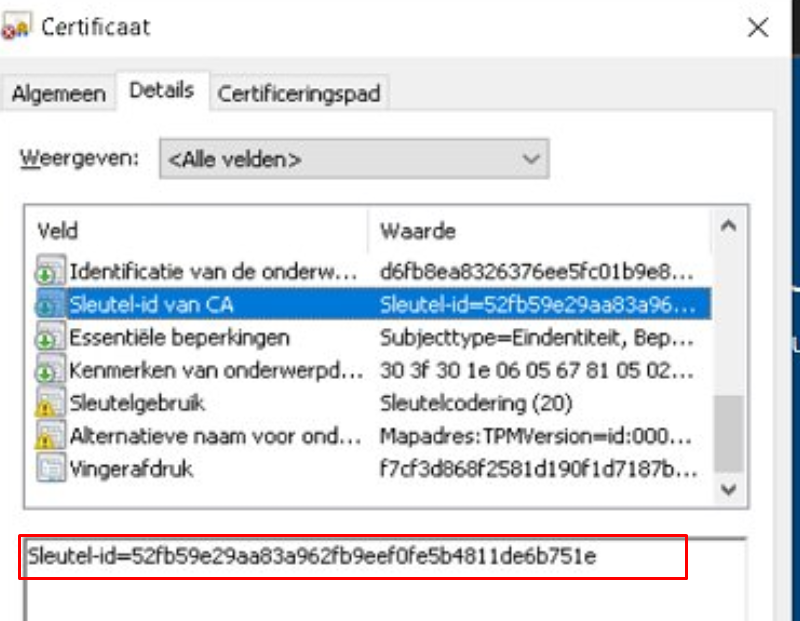
The first one: 578c545f796951421221a4a578acdb5f682f89c8
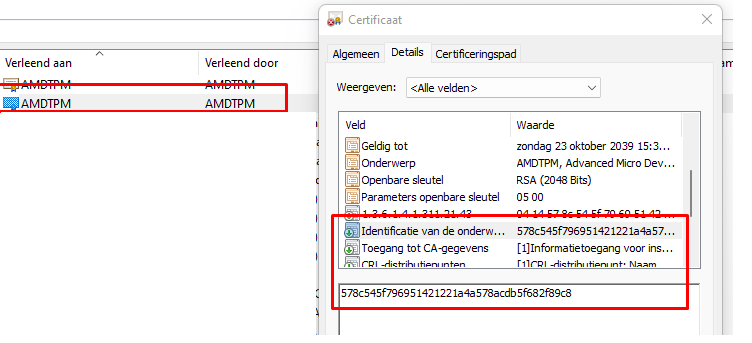
The Second one: 52fb59e29aa83a962fb9eef0fe5b4811de6b751e
*The first one:
578c545f796951421221a4a578acdb5f682f89c8:
Now, take a good guess about what the first CA issuer ID stands for
As shown above, this certificate is the AMDTPM Root CA
*The second one:
52fb59e29aa83a962fb9eef0fe5b4811de6b751e
And now for the second one!
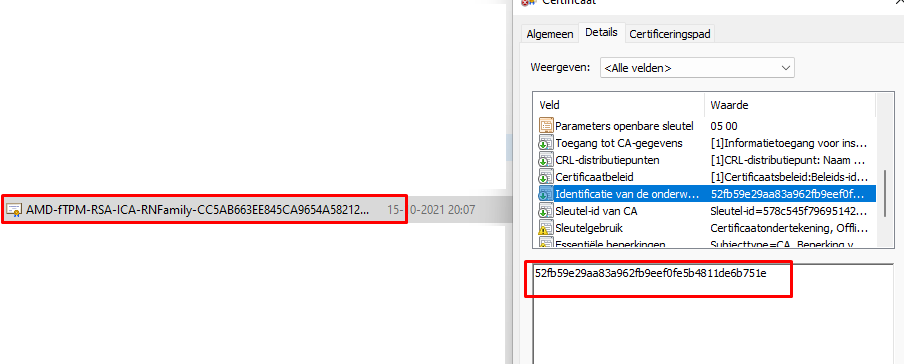
As shown above, this is the PRG-RN Intermediate Certificate ( AMD-fTPM-RSA-ICA-RNFamily)
4. Taking a better look at the certificate flow
Like I also did with the Intel TPM and Discrete TPMS, here is the flow with an AMD (f)TPM
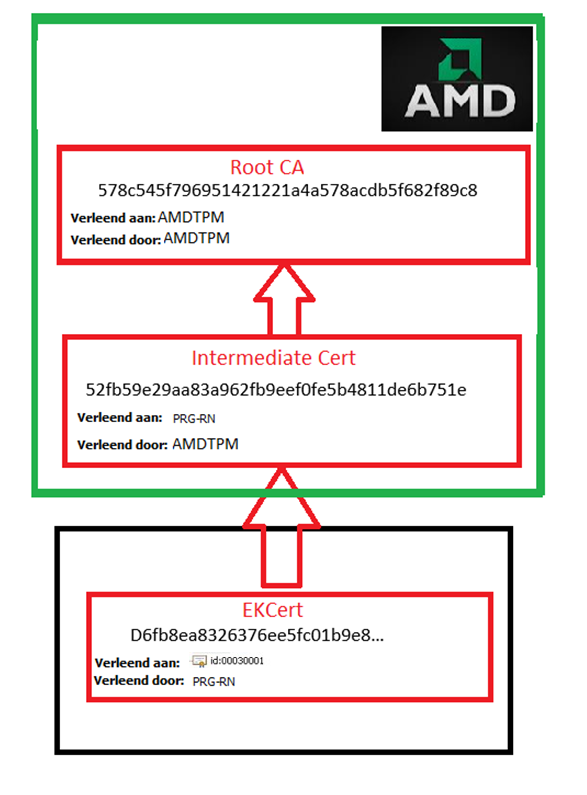
Now that we have seen the flow, I have a simple question…. Which certificate do we need?

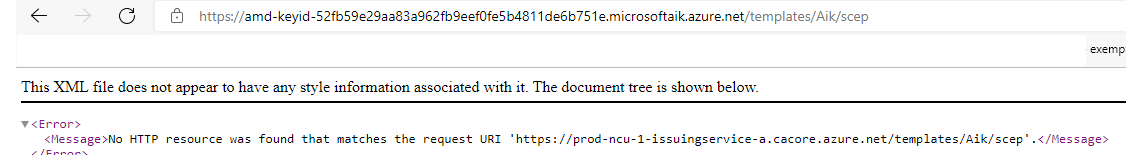
Yes!!! The INTERMEDIATE ONE, definitely not the ROOT!!!! So why the hell are we building/creating an AIK URL to the AMD Root AIK Service? That’s totally what should happen! Shall we take a look at what happens when taking a look at the URL ourselves? Just open your browser and try both of them to see what happens!
AMD Root CA
The Failing one!
Intermediate Root CA
The Working one!
5. AIK Certificate Revoked
Sometimes it’s late, and you are tired, and your brains just stop working…
In my tweet, I asked myself what was happening with the Microsoft AIK services that are older than one year… Because normally certificates are only valid for 1 year, I had the stupid idea that could be the issue why AMD wasn’t working!… stupid me…
That’s totally nonsense because the AIK certificates or signers are only replaced when they are revoked somehow. When they are revoked, the new, up-to-date, and not revoked certificate is normally automatically updated.
6. KB5022845
Last year I had confirmation that Microsoft is working on a fix and they would expect it to be released in January 2023.
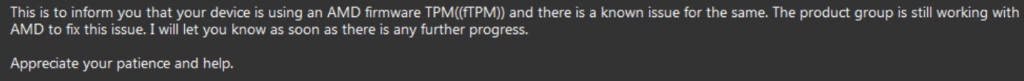
Besides this information, they told me that they would add it to the release notes. With the important Intel TPM update, Microsoft “forgot” to mention that “fix” in the release notes (still weird.. but I am no longer angry). Luckily this time it’s different. Looking at the release notes of KB5022845
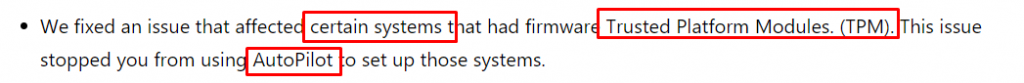
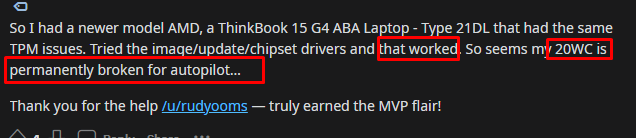
The release notes are mentioning that with this particular KB5022845, they will fix an issue that affects “Certain Systems” AKA AMD (I assume) devices, that had TPM issues during AutoPilot.
But a big but… You need to make sure your AMD Chipset drivers are up to date!.
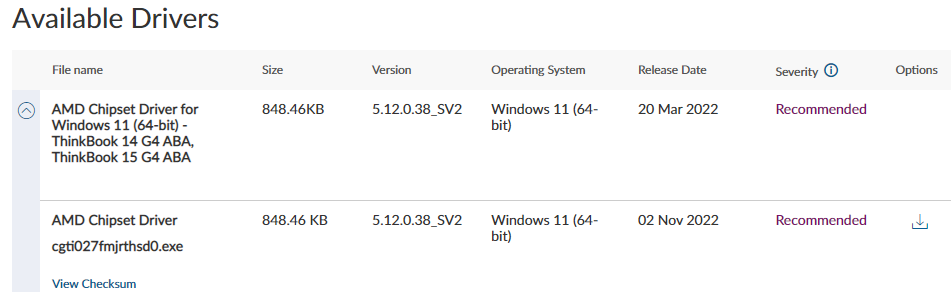
If the latest drivers correspond before this date, I guess the device doesn’t have the proper update to fix the attestation issue!
So, putting 1 + 1 together, this update, and updating the chipset drivers will fix it!
Conclusion
So Microsoft/Windows is looking at the wrong cert to get the ISSUER ID. For Intel, it needs to look at the ODCA intermediate certificate, but for AMD, it has to look at the EKCert to get the right Issuer ID.

If you are interested in the Attestation series, check them out!
Attestation and Compliance Series – Call4Cloud


Thank you for this series. It’s helped me understand the issue so much better now
How long until they fix it I guess is the next question. I know we just got the first patches for Ryzen on Win 11. I was hoping they would have bundled it in there but no luck.
There is a typo, PS cmd is: get-tpmendorsementkeYinfo -hash “sha256”
Thanx ! just updated it!
In which version of windows it does not give this error, this to do an installation of that windows and it does not crash
The fix for solving the amd issues isn’t published yet.. so we need to wat a little bit longer
Something very strange is going on. According to the MS topic it was fixed in a preview build November 15th 2021: https://docs.microsoft.com/en-us/answers/questions/537944/tpm-event-logger-error-after-cpu-swap-event-id-86.html?page=1&pageSize=10&sort=oldest
I have spent the last day installing multiple versions of Windows 11 and unless it’s because I migrated from 10 to 11 and not a clean install, the issue is still happening for me: https://i.imgur.com/btf3Rly.png
I tried the public stable, dev and insider preview builds. If they did somehow fix it in November, they must have unfixed it between end of November and the latest January 2022 builds.
Hi…a 50/50 answer… With the november update (like I am also describing in part 2) it fixed the intel tpm issue. but not the AMD… and so far as I know the code to fix it isn’t yet implemented
I get that but it seems very strange how the bleeding edge dev build of January 2022 would not for some reason include a fix that dates 2 months prior where someone said it was fixed.
To add to this, a majority of people with AMD CPUs simply don’t have this issue so what specific configuration is causing such an error in the first place? I actually once thought that maybe specific models of routers are blocking the data packets being requested?
Hi, true.. But I guess that someone was wrong 🙂 … Only the Intel part was fixed not the AMD issue 🙂 . Older AMD and Intel cpu’s didn’t have the issue as some of them just have an embedded certificate.
You could read my blogs about how the attestation URL gets created…with AMD the wrong certificate is used to build the aik URL so you would end up with an aik URL pointing to the AMD root cert in stead of the intermediate one
Good explanation – I think you’re on to something. I found this related to a new laptop upgraded to Windows 11 home. It’s a Ryzen 7 5700u ASUS, the Hyper V crashed and this message appeared related to it – creepy sudden power offs. I signed up for Insider only release preview – really wasn’t interested in going for bleeding edge for stability but starting to look like not much choice. Anyone have any updates on this?
anything new in the March updates?
Not that I have heard… This month only security updates… so I wont be expecting the AMD TPM attestation fix
https://www.windowslatest.com/2022/03/09/windows-10-kb5011487-21h2-21h1-released-heres-whats-improved/
“Fixed an issue where certificate enrollment fails”
Not related?
I am waiting for confirmation on this one 🙂
Today I installed a new (Beta) BIOS from ASUS that includes AGESA 1.2.0.7
AMD AIK errors in the event log continue.
Judging from your excellent, in depth, investigation, I assume that patches from Microsoft are also required.
Not sure why Microsoft are trailing behind AMD. I am pretty sure they would have been working together with AMD on the solution and would have received pre-releases of the microcode.
You should assume that indeed..- so far as I know the fix still isn’t released… (after months and months waiting)
Any new on those AMD certificated ?
I do still get error in event viewer
Not Found
{“Message”:”The authority \”amd-keyid-578c545f796951421221a4a578acdb5f682f89c8.microsoftaik.azure.net\” does not exist.”}
I noticed some couple of lines mentioning tpm updates in the 2022-04 update kb5012643
https://support.microsoft.com/en-us/topic/april-25-2022-kb5012643-os-build-22000-652-preview-43a75ee7-d857-4943-a2b9-f961538bd2b0
Improves the Autopilot client to process updated Trusted Platform Module (TPM) capabilities that support self-deployment and pre-provisioning scenarios.
Its worth a try to update a device with this update from the oobe screen before testing it
Has anything changed in the last week or so re: this? I ask because I was getting a daily random freeze in the OS (nothing responds, except the cursor usually), but it hasn’t happened in over a week now. I still have the same 404 error outlined in the Event Viewer due to the wrong url as you describe…so I know it hasn’t been fixed and nothing new from AMD that I can tell.
I wonder if MSFT has traced it so the OS doesn’t bork when it happens. I’ve never had BSODs from it, just a system that locks up and becomes unresponsive until I cycle it using the power button. Thanks.
thanks for information
F Microsoft F tpm !!!!!
It’s OCT 31st 2022 and has been dealing with this issue of windows freezing but the mouse still being able to semi-work while things like the start menu open but nothing will load. I have to hard restart my PC to get it to work. I have tried so many fixes with no luck.
On both 5800x and 5700x on Windows 10.
Has there been any improvement since this was recorded?
I know longer have this issue as stated up above (self-healing). Confirm you have all the latest updates for your system including OS, Video Card, and other system drivers – check AMDs website for your CPU as there are quarterly updates for anything AMD related on your machine (this may have helped with mine issue as there was no BIOS update issued from my laptop manufacturer) – this includes the AMD Software – Adrenalin Edition update tool and this – https://www.amd.com/en/support/chipsets/socket-fp5-mobile/amd-ryzen-and-athlon-mobile-chipset (this is for mine, but you may need to look up yours in their website tool). Good luck!
I have the same issue on a Win 11 VM on Hyper V.
My main problem is that I cannot connect to the LDAP CA for issuing certs…
It is now May of 2023 and Microsoft seemingly has still not fixed this. I’m going to lose my mind.
We have over 300+ Ryzen 3 4000 series Lenovo 20vg’s in our building; this specific model is the only one where attestation fails every single time. I’ve been frustrated at this for months trying to find a correlation between this model not working and the other models we have working completely fine. It wasn’t until I stumbled upon this page from a reddit post that I correlated it to being the specific processor/TPM chip being used, so thank you for all this work that you’ve done. Now I just wish the parties that be would get their shit together… I miss Apple MDM more and more each day.
Great post. June 2023. Ryzen 5900x chipset 570-E same issue :
Installed newest AMD chipset 5.05.16.529
slight difference I got .
It does check azure using the subCA subject key identifier and not the root (we have the same root).
But it still does not work
{“Message”:”The authority \”amd-keyid-907d65e9b562315997dd5ad086b2b7598957b92c.microsoftaik.azure.net\” does not exist.”}
HTTP/1.1 404 Not Found
Your subca url “the working one” .
> curl https://amd-keyid-52fb59e29aa83a962fb9eef0fe5b4811de6b751e.microsoftaik.azure.net/templates/Aik/scep
curl : {“Message”:”The authority \”amd-keyid-52fb59e29aa83a962fb9eef0fe5b4811de6b751e.microsoftaik.azure.net\” does
not exist.”}
It s not getting better…
Is there a fix for this issue already? Just wondering as it’s almost December 2023… Thanks.
I havent heard so.. let me try to find out …
It’s June 2024 any updates on this issue?
Any update on this yet? it’s 07/11/2024 and I’m STILL having this issue
so it seems.. we are also still noticing this iwth amd devices..
Happened to me on the 24h2 Update, desperately trying to fix it, its causing freeezes…