It’s really nice to see the option to apply a Label at a Team Site. When you configure the Group label options, you can make sure no guests are allowed… Really nice
I hoped after the last “automatic labelling” announcement in the Protection Portal, it would be possible to label a team site with no other options defined….. but for now, it is not… 🙁
Microsoft Cloud App Security (MCAS) or (nowadays called Microsoft Defender for Cloud Apps) to the rescue. When your license has an option to use the whole Cloud App Security suite it is possible to automatically apply a label to a team site. How Are we going to do this? By using MCAS!
1.Configure MCAS
First, you have to create a Sensitivity Label. It is wise to name it after your team site and make sure you set the encryption.
After you have created a Sensitivity Label, you can log in to the Cloud App Security Portal:
https://www.portal.cloudappsecurity.com/.
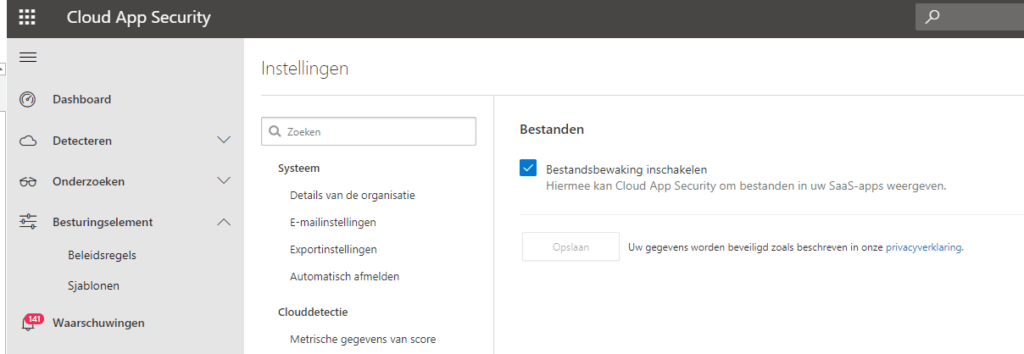
First, you have to make sure: File Monitoring is enabled on the settings page like I am showing below
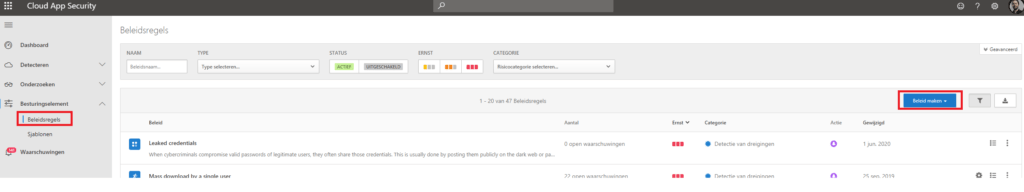
Now go back to the Portal so we can create a New File Policy, like shown below
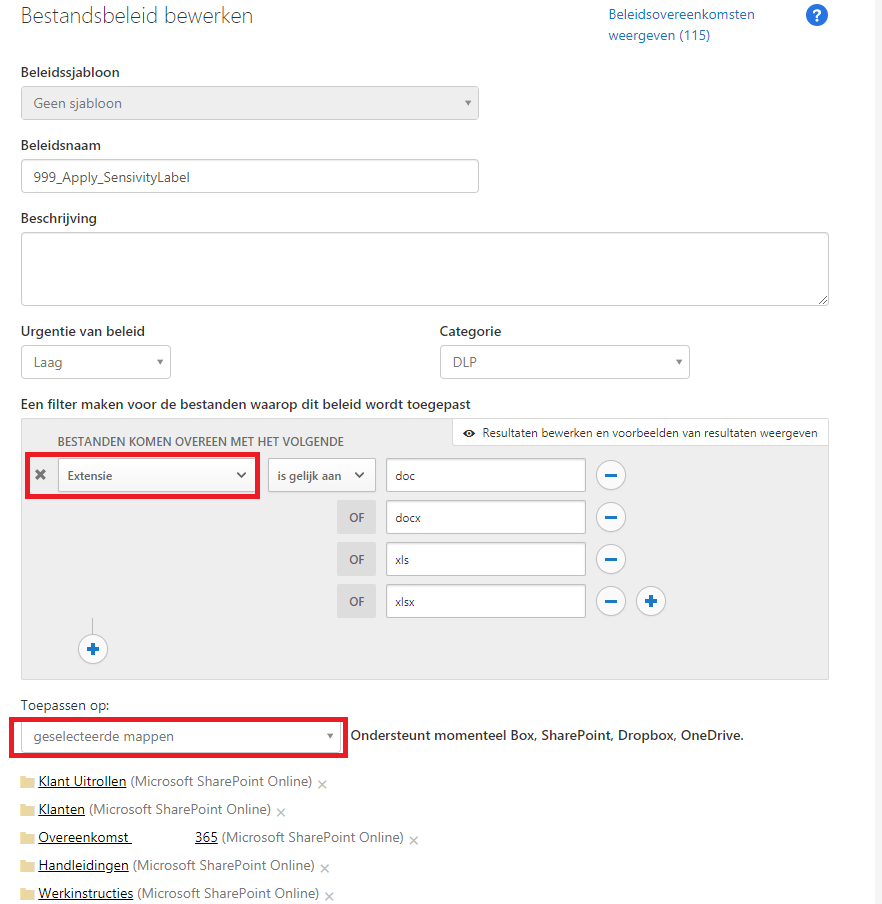
In this example, I created a filter to only apply Protection on certain extensions. Take a look at which file types are supported.
Please beware of Visio extensions, encryption works… but I have seen a lot of Visio files go corrupt. After you set the filter (optionally) you can select the folders. You can select multiple folders in a team site or just the root folder.
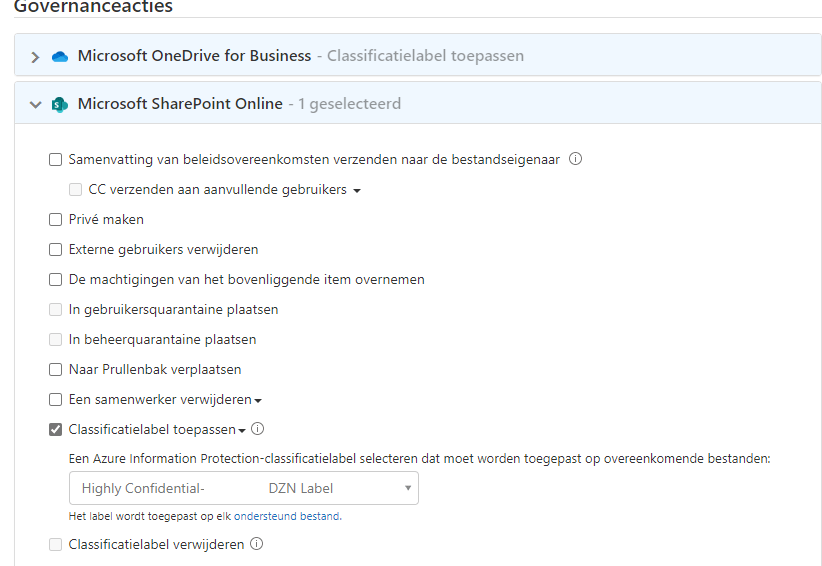
After you configure the folders, you can set the Governance Actions. Just select: “Apply Classification Label” and select the label you created at the beginning.
After you create the File Policy, please be patient… very patient. Cloud App security will apply the label at max 100 files a day (maybe now with the background tasks limitations a little bit less and it takes a little bit longer to apply…?). After the first 100, the task will be queued for the next day…
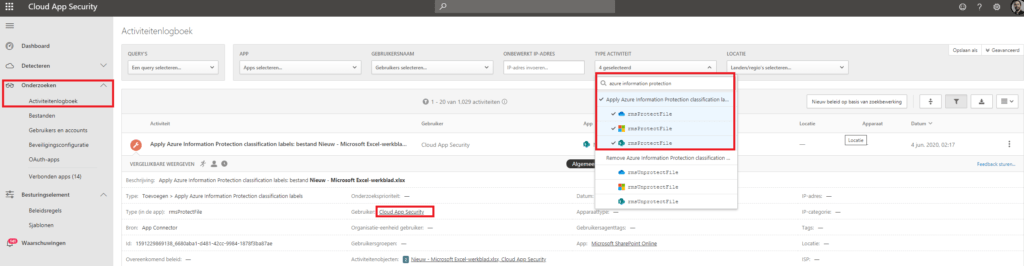
You can monitor the progress in the Activity Event log. Search for: “Azure Information Protection” in “Activity Type”. As you can see the user: “Cloud App Security” is applying the protection.
Conclusion:
I hope this will be possible in the protection portal instead of the Cloud App Security.. But for now, it works :).


One thought on “Automatic labelling Teams Data.”