Last Updated on December 3, 2021 by rudyooms
UPDATE 25-05-2021
After reading Tony Redmond's blog about this subject I rewrote this blog and added a lot of information.This blog will be about some old badass Onedrive file extension upload prevention and of course how you could monitor Onedrive.
Sometimes you don’t want specific files to be uploaded with Onedrive, like offline storage tables (ost) and maybe personal storage tables (pst)?
I am going to divide this blog into 4 parts.
1.Why you need to block these files
Some time ago I created a blog about some OneDrive/Sharepoint limitations
But looking back at this blog, I did not mention you really don’t want PST files in your Onedrive. Before I am going to show you the two options you got to make sure these files are not uploaded I am going to explain why.
Reason 1:
Most of the times PST or OST files are very big files and are used as an email archive.
When you move these files to your OneDrive it will start consuming your 1 TB (+10 GB per licensed user). Maybe a shared exchange online is a way better idea? Pst files are email, so they belong in exchange online
When you migrated the email archive (pst) to exchange online you will have some great benefits. One of them is definitely the shared access future, which you didn’t have when it was a PST file
Reason 2:
When you have attached a PST file to your Outlook account, it can’t be synced with OneDrive. Onedrive can’t sync an opened PST file because it’s locked by Outlook. Onedrive will start behaving badly.
Reason 3:
Versioning….
By default, OneDrive for Business and SharePoint is enabled for versioning for all document libraries. So when you are opening the PST file in Outlook it will update the file and it will create a new version of the file. Just like with reason 1, it will start consuming your storage.
It’s a good thing in the near future (June 28) there will be a new policy, which is on by default to permanent delete PST versions once they reach 30 days old. You can turn it off if you want?
Set-SPOTenant -DisableOutlookPSTVersionTrimming $False
But to mention it again… these files don’t belong in Onedrive!
2. How you can block or prevent these files
You have got multiple options to make sure these files are not uploaded.
- The Onedrive Admin center (server-side)
- Intune: CSP/Administrative Template or settings catalog (client-side)
2.1 The Onedrive Admin center (Block Modus)
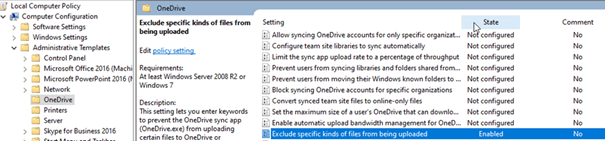
Excluding extensions in the Onedrive admin center was the way to go to make sure some files are not synced with Onedrive.
You could configure these settings in the sync settings tab:
OneDrive for Business Admin Preview
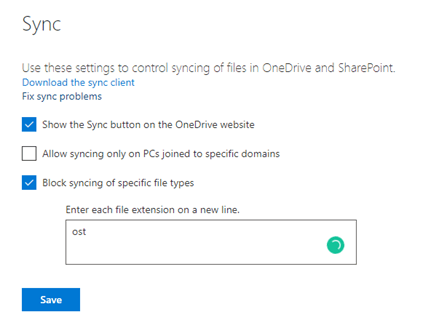
When configuring the rule like above, it will apply to all existing files. Onedrive could stop syncing because there are many sync errors. You will need to manually remove these files to make sure Onedrive will keep syncing the files as it should.
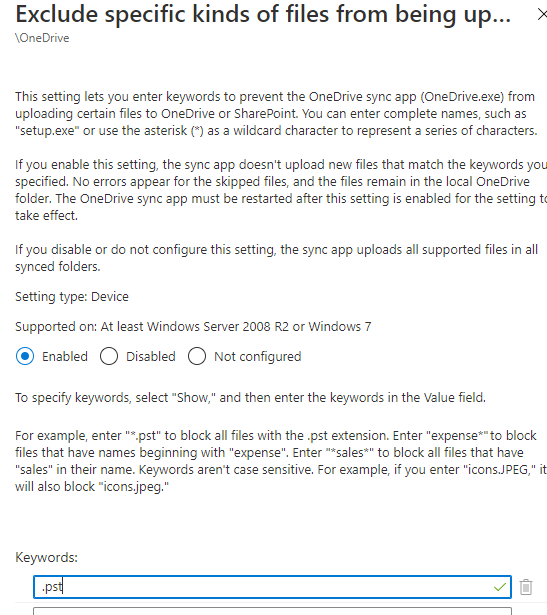
2.2. Intune: CSP/Administrative Template (Exclusion-Mode)
There must be another way… And yes there will be, with the latest insider Onedrive (version 20.201.1005.0006) you will get a new adml file. Just open the C:\Program Files (x86)\Microsoft OneDrive\20.201.1005.0008\adm\onedrive.adml file.
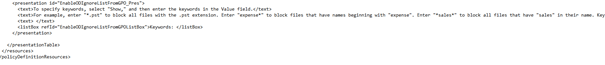
Did you notice the “EnableODIgnoreListFromGPOListBox” key? That’s very cool. You can configure it in your group policy (but it’s not working yet)
UPDATE 25-05-2021 (OF COURSE IT’S FIXED BY NOW!!)
I was wondering if I could create the necessary policy in Intune. This setting “was” not available in the Intune Administrative Templates …
2.2 Option 1: CSP
First, we need to do some admx ingesting.
Just like I did when the “forcesync” was not yet available in Intune. Create your own custom admx file and create a new custom made device configuration policy.
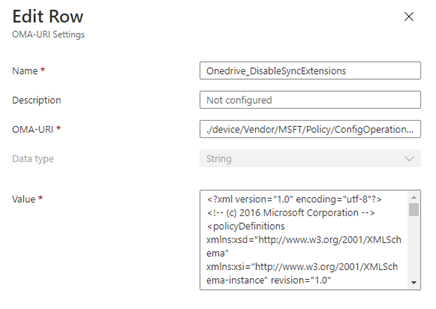
-OMA-URI: ./device/Vendor/MSFT/Policy/ConfigOperations/ADMXInstall/OneDriveNGSCv2/Policy/OnedriveDisableExtensions
-Data Type:
String
-Value:
<?xml version="1.0" encoding="utf-8"?>
<!-- (c) 2016 Microsoft Corporation -->
<policyDefinitions xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" revision="1.0" schemaVersion="1.0" xmlns="http://schemas.microsoft.com/GroupPolicy/2006/07/PolicyDefinitions">
<policyNamespaces>
<target prefix="OneDriveNGSC" namespace="Microsoft.Policies.OneDriveNGSC" />
<using prefix="windows" namespace="Microsoft.Policies.Windows" />
</policyNamespaces>
<resources minRequiredRevision="1.0" />
<categories>
<category name="OneDriveNGSC" displayName="$(string.OneDriveNGSCSettingCategory)"/>
</categories>
<policies>
<policy name="EnableODIgnoreListFromGPO" class="Machine" displayName="$(string.EnableODIgnoreListFromGPO)" explainText="$(string.EnableODIgnoreListFromGPO_help)" presentation="$(presentation.EnableODIgnoreListFromGPO_Pres)" key="SOFTWARE\Policies\Microsoft\OneDrive">
<parentCategory ref="OneDriveNGSC" />
<supportedOn ref="windows:SUPPORTED_Windows7" />
<elements>
<list id="EnableODIgnoreListFromGPOListBox" key="Software\Policies\Microsoft\OneDrive\EnableODIgnoreListFromGPO" additive="true"/>
</elements>
</policy>
</policies>
</policyDefinitions>
Now we have the admx file implemented, we can configure the extensions we need to block.
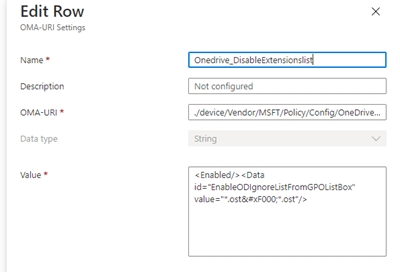
OMA-URI: ./device/Vendor/MSFT/Policy/Config/OneDriveNGSCv2~Policy~OneDriveNGSC/EnableODIgnoreListFromGPO
Data Type:
String
Value:
<Enabled/><Data id="EnableODIgnoreListFromGPOListBox" value="*.ost*.ost"/>
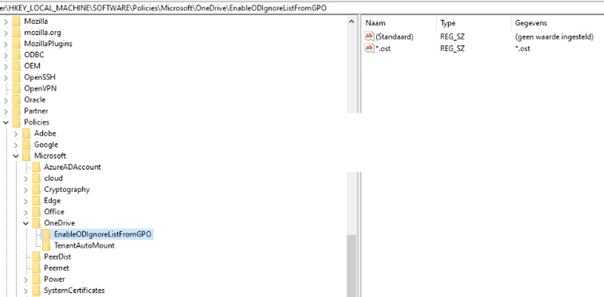
Now we need to have some patience until the key is pushed to your device. Open regedit to check if the key is created in: Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\AdmxDefault\40CB1E11-CF17-4DF8-A7EC-DBDBCFC9CA7B\OneDriveNGSCv2~Policy~OneDriveNGSC\EnableODIgnoreListFromGPO
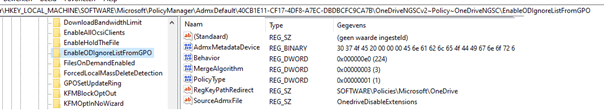
Also, check if the policy itself is also created.
2.2 Option 2: Administrative Templates
I am very glad you could now define this setting inside the administrative templates instead of creating your own CSP (even when it’s fun to do so )
I hope the OneDrive settings will also appear in the settings catalog.
3. Results
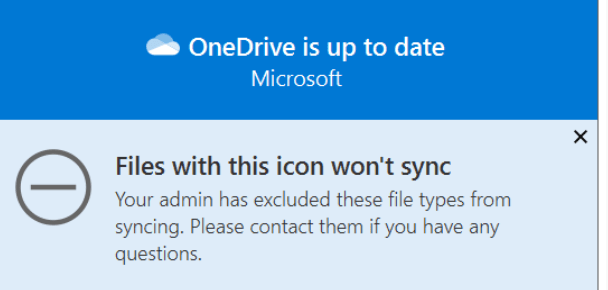
Comparing both solutions, the client-side and the server side you will notice one big difference.
Client Side –> New files

Server Side –> Existing Files
I would choose the Client-Side because when you don’t know if there are PST files in Onedrive and you start blocking it, you could end up receiving a lot of phone calls.
4. Monitoring Onedrive
Monitoring OneDrive can be really hard, some time ago I wrote a blog on how to do so by using the Onedrive log file
Conclusion:
It’s very cool there will be another option to prevent some file extensions to be synced with Onedrive. And the possibility to start monitoring Onedrive… I like it a lot.


