This updated blog will be an additional one, to the one that Michael Niehaus wrote about when a device sync with Intune .
In this blog, I will examine the same things as Niehaus but this time the next-generation Intune, MMP-C. I will also examine the sync scheme and show you all the strings attached.
1. Introduction
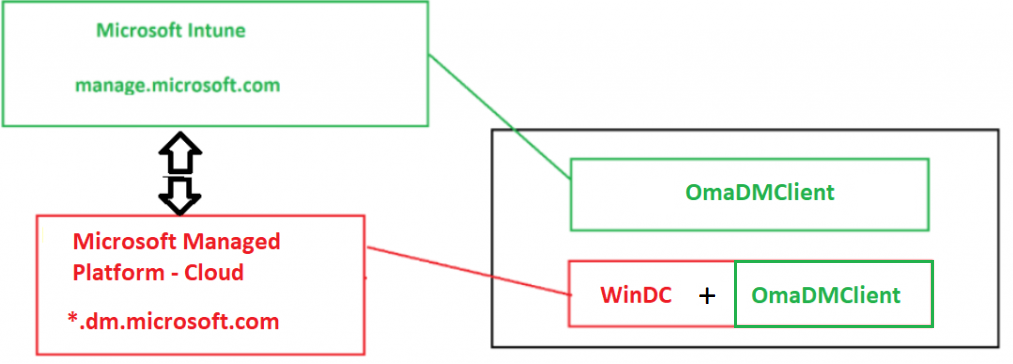
After noticing and reading Niehaus’s “When Does a Device Sync with Intune” blog, I felt obligated to update this blog. Instead of the good old Intune itself I will focus on the next-gen Intune. This Next-Gen Intune is a piece of infrastructure that is being placed next to Intune itself and is called MMP-C (Microsoft Managed Platform – Cloud )
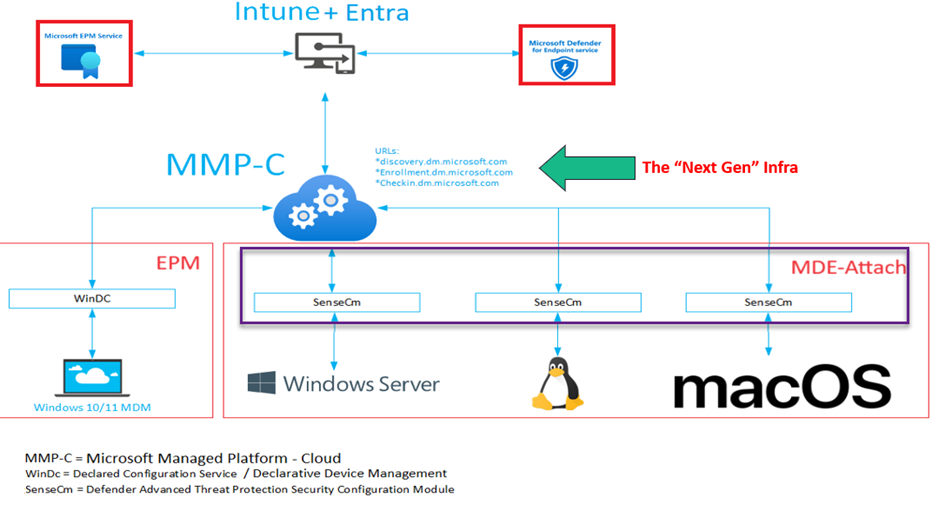
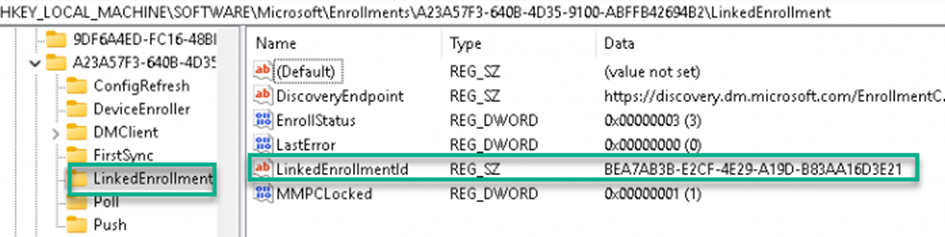
The MMP-C enrollment depends on your Intune enrollment and during enrollment it will get linked to your good old Intune enrollment.
For now, the MMP-C enrollment will only happen if you have purchased the Intune Suite to start using Endpoint Privilege Management (EPM)
If you purchased the Intune Suite (nothing more!) all of your devices will automatically get onboarded to MMP-C and will get linked/dual enrolled. This will happen automatically, and you will not notice anything about it! (of course, when everything goes according to plan)
Once the device gets the dual enrollment, the EPM agent will show up on your device, and with it, you can start elevating processes. To ensure you can elevate some processes, you need to create some elevation rules in Intune.
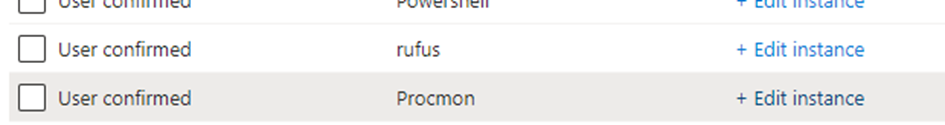
After configuring the EPM policies, the elevation policies will be delivered to the device, the next time it checks in/ sync. So when does this sync happen?
2. When Does MMP-C sync?
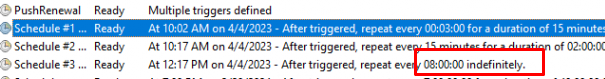
With the new enrollment, we also have the same schedules we had with the Intune enrollment. These schedules were brought to life to sync some new policies.
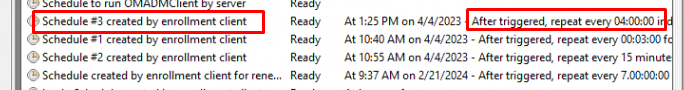
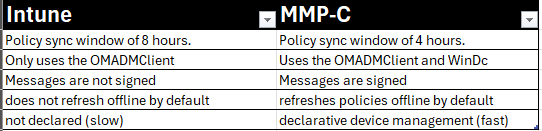
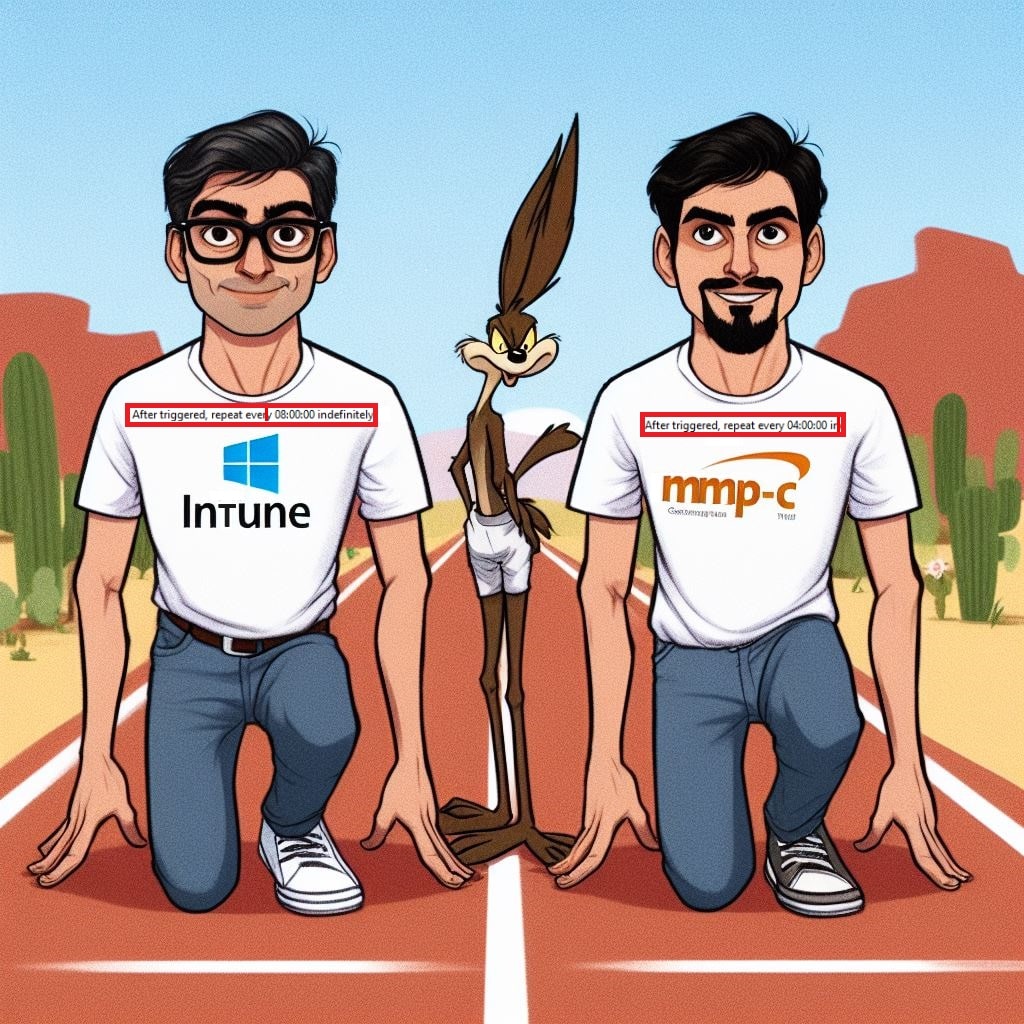
The biggest two differences here are that schedule #3 is repeated every 4 hours instead of the 8 hours we have with the default Intune enrollment.
Besides the smaller sync window than the Intune one, performing a sync with MMP-C is finished within a few seconds!! So who will win the “sync race” Intune or MMP-C???
These schedules will make sure your device will be synced with the latest policies. The MMP-C schedule #3 is the one responsible for syncing the policies with MMP-C. (For now, only the EPM Elevation rules and policies)
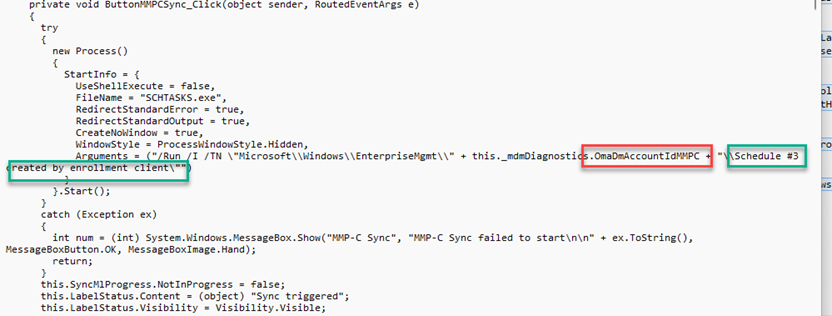
When we want to manually kick off the MMP-C sync, we need to execute the scheduled #3 task. Another option would be to use the SyncML Tool. With one of the latest releases, a nice new button showed up: MMP-C Sync

If we take a closer look at what this button does, we will notice that it will kick off the same scheduled #3 task I mentioned before. The Syncml tool tries to find the proper scheduled task that corresponds to the MMP-C Enrollment and would kick off the sync.
Schedule #3 would kick off the OmaDMClient. Should we take a look at this one first to better understand it?
3. The Schedule Flow
Let’s start by looking at what happens when we execute “Schedule #3 created by enrollment client” I have created a simple flow explaining how Schedule #3 finally calls up on the schedule to run OMADMCLIENT (phoneprovider) by client.
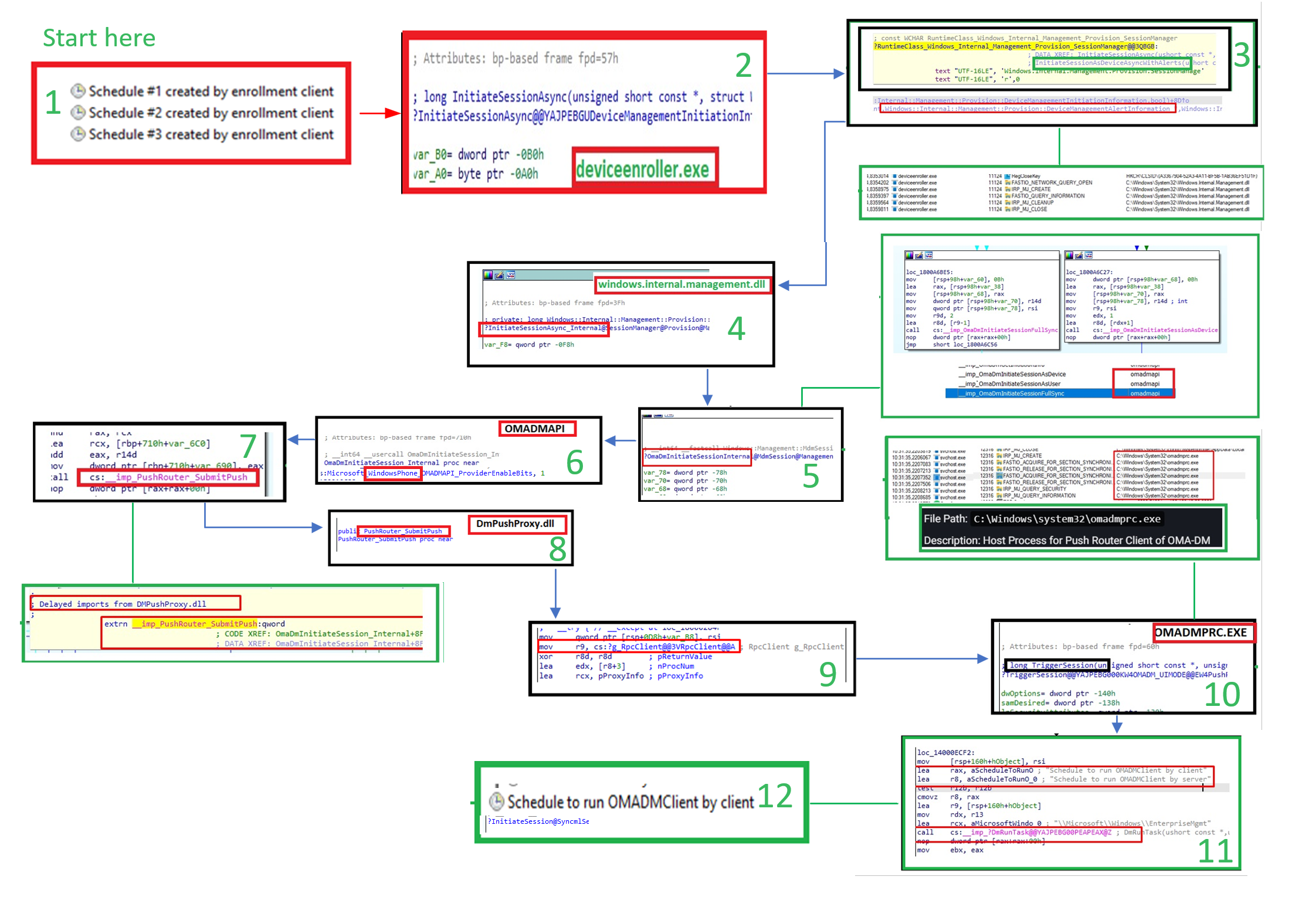
But besides the OMADmclient that gets executed, something else is joining the sync party! So keep on reading!
4. Dcsvc.dll
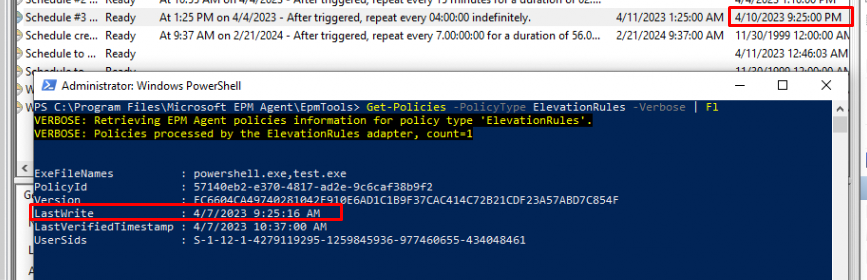
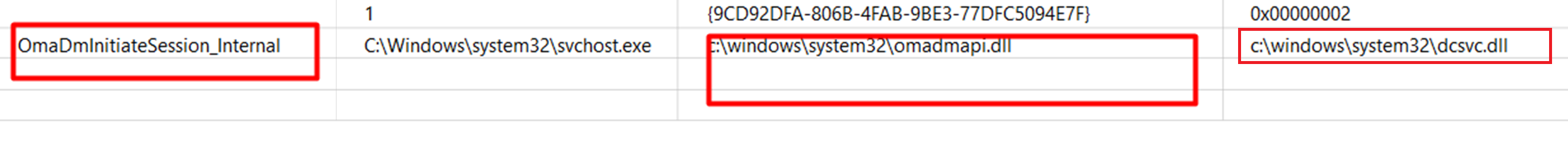
Every 4 hours schedule #3 would kick off the OMADMClient.exe with some parameters. By comparing all the logs/traces I got with the deviceenroller.exe and the OMADMCLIENT, I noticed that the omadmclient calls upon a DLL called: dcsvc.dll (Declared Configuration)
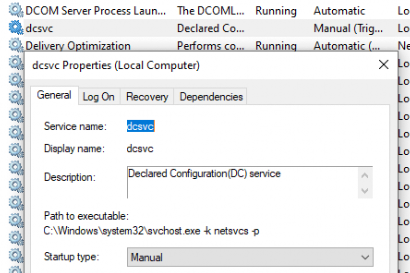
At first, it didn’t ring any bell but if you take a closer look, you will notice that the description mentions a bit more: Declared Configuration (DC) service (dcsvc.dll)
Besides the DLL files, we will also notice the same when the device performs a WCOS check-in at the MMP-C service. In this body of the post, we will notice an XML
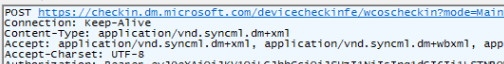
This XML contains something called the DeclaredConfiguration schema
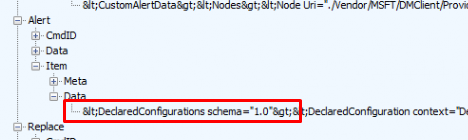
When looking at the corresponding response we got in Fiddler, we will also notice the same declaredconfiguration being mentioned with some nice WinDC Documents
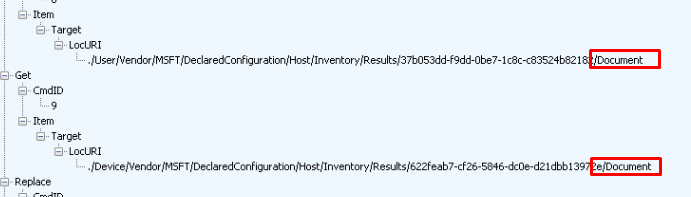
When syncing the device, the “Declared Configuration Documents” with the settings (Epm Elevated MSFTPolicies) will be delivered to your device. Shall we take a look at what happens under the hood when we are syncing our device with MMP-C?
5. The MMP-C Sync Flow
I turned all logging on (Procmon/Fiddler/Syncml/WPR trace/Event log Debug logging) and this is what I got! It should explain the dependencies of the whole process and should give you an insight into what happens when your device syncs with MMP-C to fetch the latest policies.

As shown above, at the end and after waiting a couple of hours schedule #3 (OMADmClient) kicks in and delivers the elevation policy test.exe (DC Document) to the device with the use of the Declared Configuration Service
I guess it is safe to say that besides the OMADmClient that gets executed with the schedule #3, the WIndows Declared Configuration (windc) is added on top!
6. The Forgotten Refresh schedule?
Now we have taken a closer look at Schedule #3, we also need to take a look at a different schedule which isn’t mentioned anywhere in the Intune Enrollment. I am talking about the “refresh scheduled created by Declared Configuration to any setting changed on the device” scheduled task.
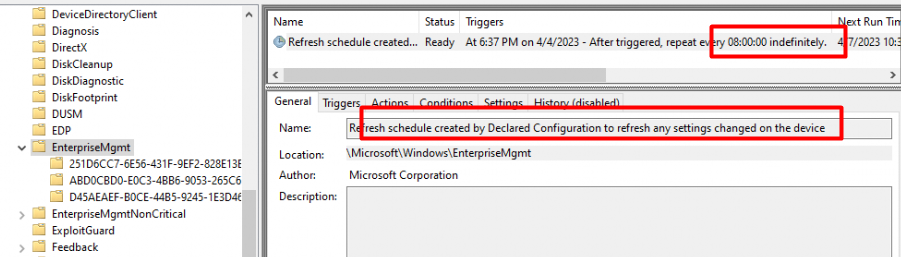
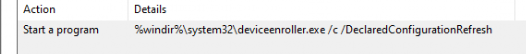
This refresh schedule would kick off the deviceenroller.exe (always that damn executable!!!) with the /DeclaredConfigurationRefresh parameter.
After spending some more time looking at the WinDC and the EPMAgentService, I decided to create a dedicated blog post series to this scheduled task to explain it all.
WinDC | Epm Policies | Refresh Schedule | MMP-C (call4cloud.nl)
When you have gone through all of those blogs, the first thing that could come to mind would be:

Rudy, that just sounds like Config Refresh. yeah!!! The refresh schedule created by the declared configuration to refresh any setting changed on the device is Config Refresh on steroids!
Conclusion
It’s pretty obvious that the next gen infra called MMP-C is the future and could eventually replace Intune.If you don’t believe me, take a look at this simple overview.


I’m curious about the tenant enrollment for MMP-C when using Apple DDM since I don’t believe that’s part of the Intune suit. Does it just not enroll the Windows devices until Intune Suite is purchased for EPM?
Apple DDM and Microsoft its DDM solution (windc) are 2 seperate things.. WinDC is on the device and the service itself where it will communicate with, needs to be onboarded (enabled) to your tenant. For now activating the intune suite, does exactly that
So if I buy one license och test Intune Suite the whole tenant will be onboarded? 🙂
Hehehe…. well m… yeah … 🙂 as you can’t scope it… back in the day, the device would only be onboarded when you scoped the epm policy