Last Updated on December 2, 2021 by rudyooms
This blog will be about Chromebooks and MAM. I will also introduce a colleague of mine. He will co-author my blogs from now on, this will be our first joint effort. His name is Mark Uijtdewilligen. Please follow him on LinkedIn: Mark Uijtdewilligen | LinkedIn
Today we received a call from a customer who wanted to buy Chromebooks. Our first reaction was “Huh? Why?” (his company is currently undergoing a transformation from a remote desktop environment to a modern MS365 environment. They already began their first step by already enrolling all newly purchased devices to become Azure AD joined.
So we asked him, why Chromebooks? Surely if you choose the Microsoft 365 platform you want to have Windows desktops/laptops so you can have a compliant device with all the bells and whistles?
Turns out they have a lot of frontline workers who occasionally work on a computer. Now that working from home has become a part of almost everyone’s job (and it’s not going anywhere folks), his company wanted to provide their workers with the means to do so while also being able to connect to a workspace at the office and use their device there. But the reality of the situation is that COVID hit a lot of companies pretty hard. So, the budget was a concern here. For the price of 1 decent laptop, he could buy multiple cheaper Chromebooks.
This made us look at the situation from a different angle. We always try to focus on things like security and a top-shelf user experience. But what if for some workers… A less convenient way is also acceptable. Maybe they use a platform they like that doesn’t always fully support all the MDM features? Or maybe they just want to be able to work on their own devices.
And just like Andy Malone was telling us on the last Cloud conversations podcast with Ru and Pete
“You don’t have to use a pc, you don’t have to use windows, you can make use of all the Microsoft Apps but you can consume it on another platform”.
So why not use a Chromebook we thought?
But here comes the trouble. A Windows 10 device could be enrolled into Azure Ad and Intune, but did you ever try to enrol a Chromebook into Azure/Intune? Let’s try to download the Company portal from the play store and start with open Microsoft Word to begin the enrolment process.
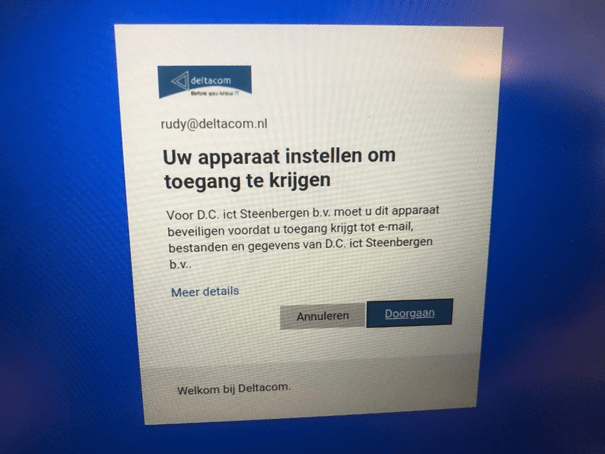
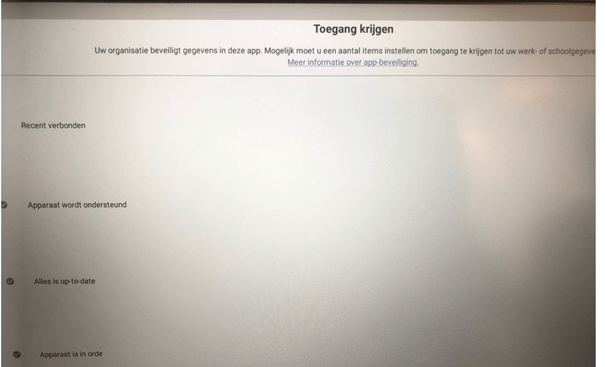
But after entering the MFA challenge this page is going to popup
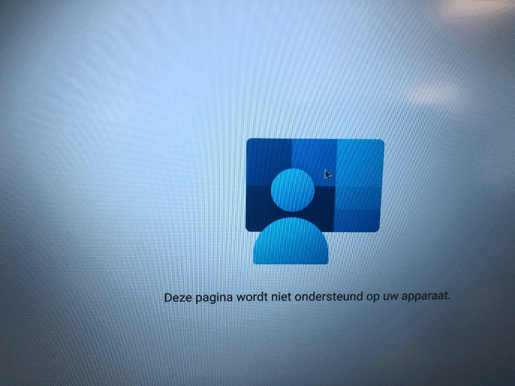
It looks like the Company Portal App is aware of the fact it’s ChromeOS and not Android, so you could let go of the hope to enrol the device.
But fortunately, this doesn’t mean you can’t use a Chromebook!
There are a few steps you need to take before you could still access the MS365 data with the desktop apps from a Chromebook in a secure way.
- Loosening the security in the conditional access rule to require compliant devices
- Creating an App protection Policy for unmanaged devices
- Making sure your conditional access rule is in place to require App protection/Approved Apps
- Monitoring the App protection and making sure Teams governance is applied
- Making a Testdrive
- Selective wipe the Chromebook
1.Loosening the security in the conditional access rule to require compliant devices
In a normal situation, we are telling our customers that all the devices which need access to Microsoft 365 need to be enrolled. The conditional access rule in our baseline policy to require compliant devices to access Microsoft from the desktop apps will also prevent a Chromebook to access the Microsoft 365 with the desktop apps. So we need to make some changes in this Conditional access rule as shown below.
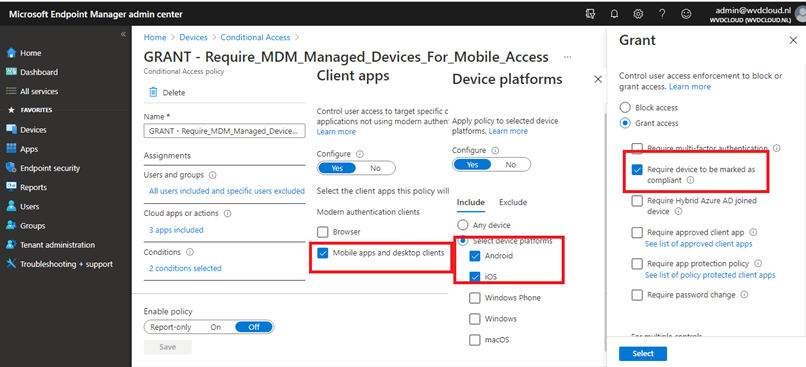
You will notice I am requiring Android devices to be compliant, so for now let’s remove Android from the device platform selection.
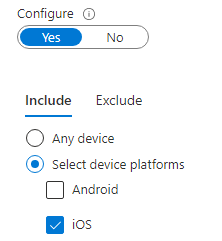
Now we have loosened the security for android devices we need to make sure we also have App protection configured.
2.Creating an App protection Policy for unmanaged devices
Rudy has created a blog about this topic some time ago. I advise you to read his blog first before we continue.
After you have read this blog, you will know what you need to do to make sure an App protection policy is in place to protect your Apps. So, let’s create the app protection policy.
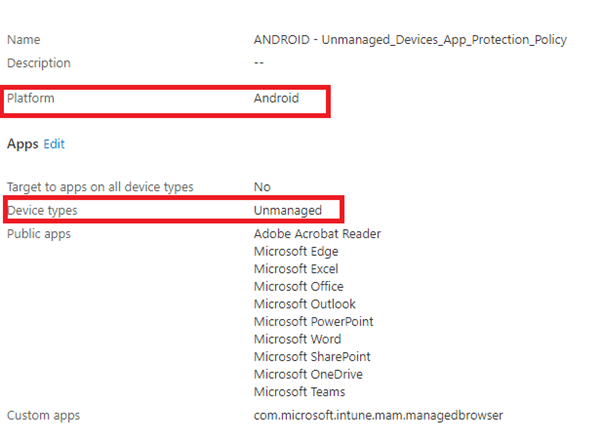
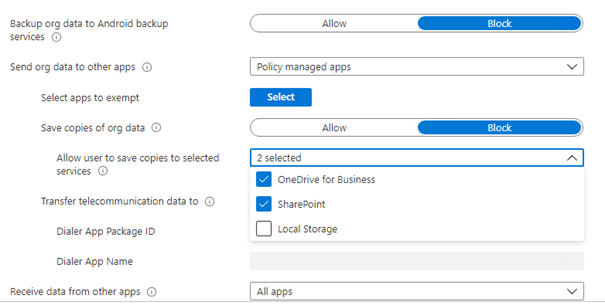
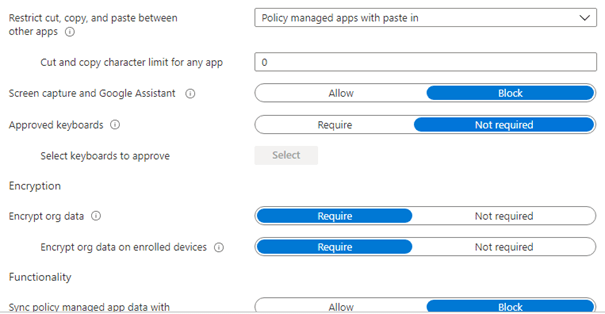
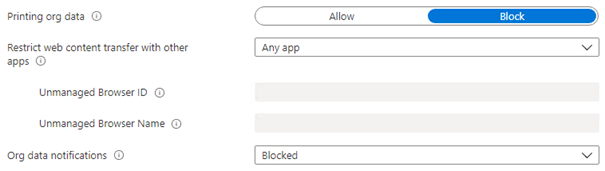
And the data protection Settings. Of course, this is just an example. But in our opinion saving copies of original data to the local storage must not be allowed in any way!
Maybe you have read his other blogs about app protection. In one of them, Rudy shows how you could configure the App protection policy to make sure when a user account is disabled the data is wiped from the device.
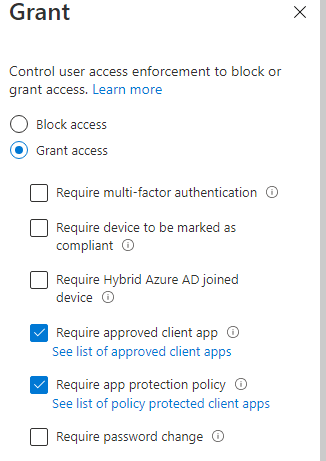
3.Making sure your conditional access rule is in place to require App protection/Approved Apps
When you are configuring app protection policies, you’ll need to create another barrier/firewall to make sure app protection will be applied. Of course, this could be done with Conditional Access. Again, Rudy made a blog about this subject some time ago. It will also tell you how to deal with the “or” switch.
Just create another Conditional access policy and target the proper platforms/client apps and require App Protection or an approved app as shown below.
4. Monitoring the App protection policies and Apply teams governance
Monitoring
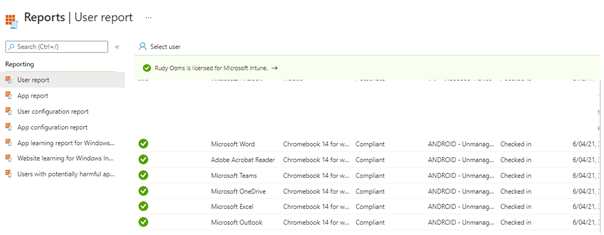
But only relying on the conditional access policies is not best practice you will need to make sure you could create some reports to stop worrying about yourself. And like always, 🙂 there’s a blog about this one as well. It will show you how to troubleshoot and how you could make sure you are in control.
Now we know how to create an App protection usage report… let’s create one for ourselves to see how it detects our fantastic Chromebook.
Teams Governance
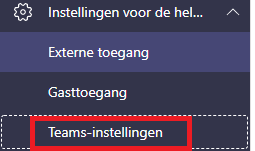
When everything is configured and secured, you must not forget to apply some teams governance. When you are making sure you are preventing file download, please also apply some teams governance.
Open your Teams admin center and open the teams settings.
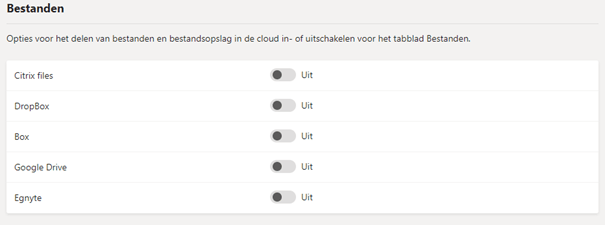
And make sure you remove all the File options out there! (of course, only when you don’t use them).
5. Making a test drive
It’s time to take a test drive with this new shiny Chromebook. Install all the apps needed.
Open Onedrive and you will notice the app needs to be protected! And it will ask you for a pin!
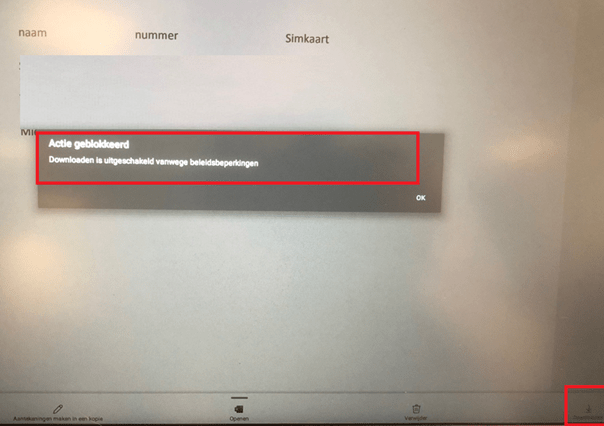
Now we know Onedrive is secured with an app protection policy try to download a file to the local storage. You will notice it will be blocked because of a policy restriction!
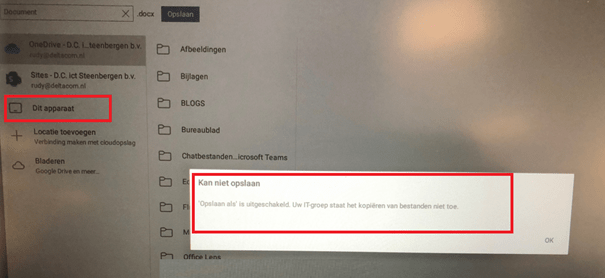
Okay, but what happens when you want to save an existing file in Word to the local storage? No sir! Your IT department won’t have it.
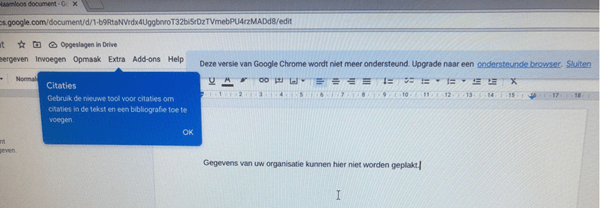
Cool! We noticed we couldn’t download anything, but let’s copy-paste the whole document into the building document app from the Chromebook. It tells us, the company data could not be pasted. Now the picture is complete…
6. Selective Wipe the Chromebook
Now we have seen how to implement it/monitoring it/testing it. How are we going to make sure the device which is not azure ad joined nor registered is cleaned when we want it to be?
Ow no… I guess we’ll need to point out another blog. It will show you all the wipes you need to know about…
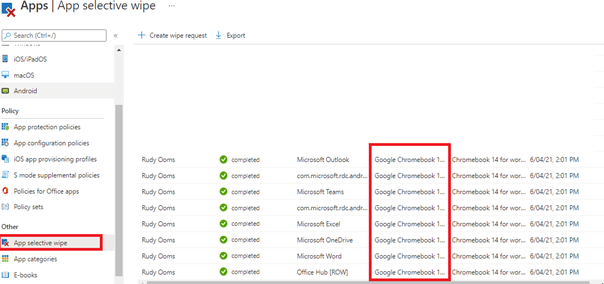
Now we know, we will need to perform a selective wipe… let’s do so by selecting the username and the device which is in need of a selective wipe!
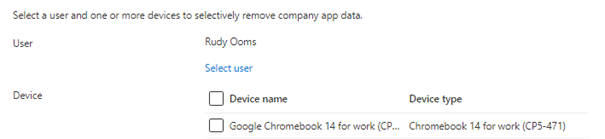
Select the proper device and have some patience.
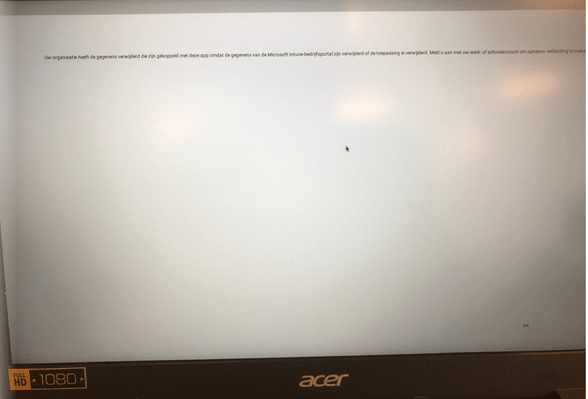
And your Chromebook will end up with this warning: Your company has deleted the data which was attached to this app and you have the sign on again to establish a new connection.
Conclusion
In an ideal world, we’d all be working with compliant Windows 10 devices with the full power of MS365 enabled on each device. But part of what makes IT so much fun is coming up with creative solutions to what (at first glance) may seem like weird questions or ideas. The reality of the situation is that a lot of companies make IT choices based on a (tight) budget or personal preference for a certain type of device. We should enable them while still making sure these devices pass the security measures we put in place.
P.s: After creating this blog, I noticed Thijs Lecomte also did a blog about this topic 🙂
Can Chromebooks be managed with MEM? – 365 by Thijs

